This month we’ve been targeted by a spear phishing attack: an attempt to scam us out of thousands of pounds.
In short, someone pretended to be Adrian and sent an email to Manuela, our finance assistant, to ask her to transfer a sum of money to a “new supplier’s” bank account.
It was cleverly put together – the email appeared at first glance to come from ‘Adrian Barkey’ and replies were edited to make it look even more realistic. The scam failed because we don’t have a singular point of approval for financial activity like this – a secondary confirmation is required.
If a supplier sends us an invoice with new bank account details, we get in touch with them using contact details from an old invoice to make sure the request is valid.
How to avoid spear phishing attacks
- Every person in your organisation must understand the risks and best-practice
You could have the most sophisticated anti-spam, anti-virus, anti-hacking software in place, trained almost everyone in cyber-security – but if there is one person who missed the message then you are at risk. It’s a cliché, but a chain is only as strong as its weakest link. - Insist on a second level of checking for anything sensitive
Passwords, granting access to new users, payments to new bank accounts or suppliers, building access codes – all of these and anything similar should never be given out without absolute assurance that you’re definitely in touch with the correct person. A secondary level of validation by text message, telephone call or in-person is essential. Text messages should only be considered valid if there is a conversation history included with it. - Don’t use email to transfer sensitive information
Use a service like LastPass to securely share passwords to joint accounts, and a separate, secure messaging service to communicate confidential information and requests. - Be suspicious
Just because something lands in your inbox doesn’t mean it is genuine. Apply a reasonably degree of suspicion to any communication, especially if you’re being asked to do something. If you’re asked to, for example, log into a PayPal account, don’t click on the link in the email even if you think it’s genuine – go to the PayPal website directly and log in from there.
- Don’t create bad habits
Don’t send emails asking staff or colleagues to transfer money, share passwords etc. – it will create a habit and assumption within your organisation that it’s fine to do. In the same way, don’t routinely share your account credentials so that colleagues can process your email or edit your documents; in most cases there are effective, secure solutions that can be implemented quickly and easily. - Understand the basics
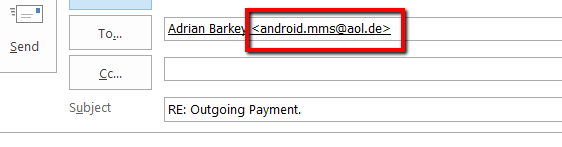
When you click reply to an email, take a moment to check the email address it’s going to. Here’s a screenshot from the scam email we received – after clicking reply you can clearly see that the address is not adrian.barkey@ejc.it – an immediate warning that something is amiss.
- Extra email security services
There are services available – part of the Mimecast email solutions we provide – which will help prevent or flag-up if someone is pretending to be a member of your organisation, or if other red flags are spotted. Mimecast’s Targeted Threat Protection would have blocked our example above. Talk to us if you’re interested.


